Software systems today rarely operate alone. Businesses use multiple platforms to manage customers, finances, operations, analytics, and communication. These systems must exchange information to keep operations running smoothly. The technology that allows these platforms to communicate is the Application Programming Interface, commonly known as an API. APIs allow software applications to request, send, and update information between systems without manual intervention.
For service companies that rely on digital platforms, APIs are essential for building connected workflows. A field service platform may exchange data with accounting software, inventory systems, customer relationship management tools, reporting platforms, or equipment monitoring systems. Each integration improves efficiency by ensuring that data flows automatically between systems. However, whenever information moves between platforms, security becomes a critical concern.
Why API Security Matters
API integrations handle sensitive operational and customer information. If these connections are not properly secured, they may expose data to unauthorized access or manipulation. Protecting API integrations therefore becomes an important responsibility for organizations that rely on digital infrastructure. By following well established security practices, businesses can ensure that their systems remain connected while keeping their information protected.
How APIs Work
Understanding API security begins with recognizing how APIs operate. When one system wants information from another, it sends a request to the API. The receiving system verifies the request and returns the requested data if the request is authorized. Without proper safeguards, any system could potentially attempt to request information. This is why authentication and authorization are fundamental components of secure API design.
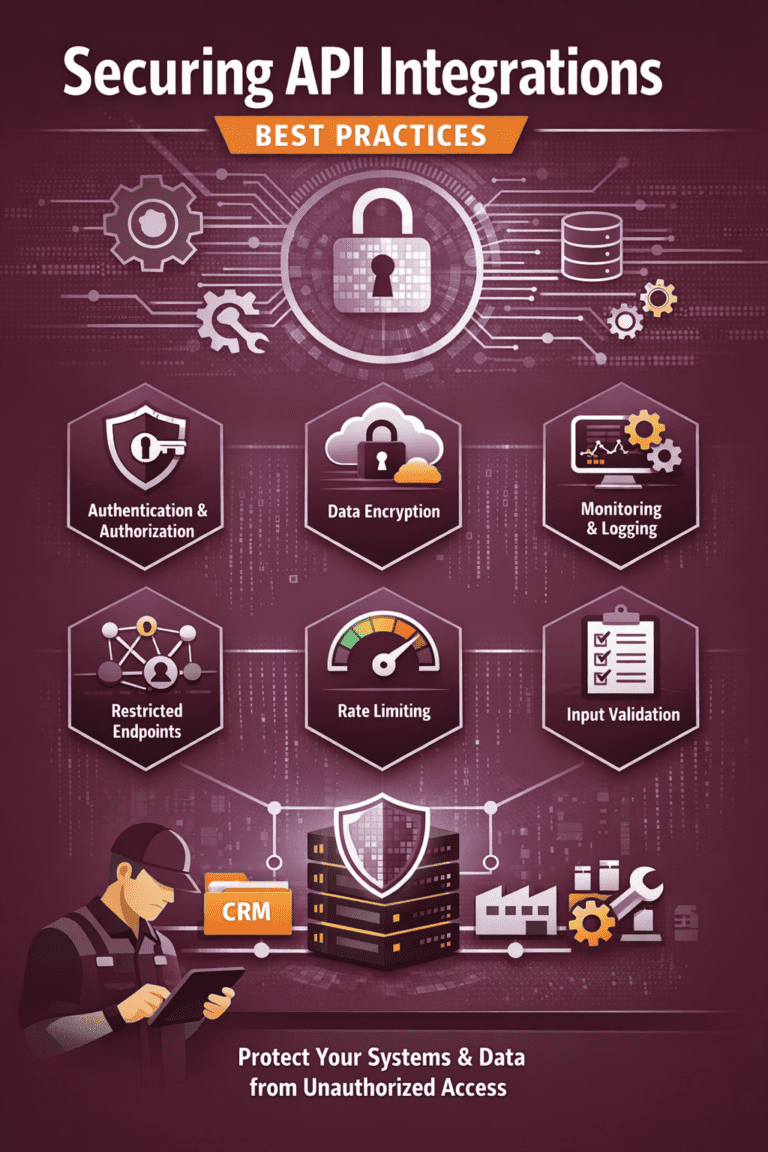
Key practices for securing API integrations
Authentication and Authorization
Authentication ensures that the system making the request is legitimate. Before allowing access, the receiving platform verifies the identity of the requesting system. This is commonly done using secure tokens or keys that function as digital credentials. Each integration receives a unique credential that must be included in every request. If the credential is missing or invalid, the request is rejected. This process prevents unauthorized systems from interacting with the API.
Authorization goes one step further by controlling what authenticated systems are allowed to access. Not every integration should have access to all data within a system. For example, an accounting system may need information about completed work orders and service charges, but it does not need access to technician schedules or internal operational notes. By defining clear authorization rules, organizations ensure that each system only accesses the information necessary for its function.
Data Encryption and Storage Security
Encryption is another essential security measure for API integrations. When data travels between systems over the internet, it passes through multiple networks before reaching its destination. Without encryption, this information could potentially be intercepted. Encryption converts the data into a coded format that cannot be read without the proper decryption key. Most modern APIs use secure communication protocols to ensure that all data exchanged between systems remains protected during transmission.
In addition to encryption during transmission, secure systems also protect data while it is stored. Databases containing service records, customer information, and operational data must use strong security measures to prevent unauthorized access. Secure storage practices help ensure that even if a system is compromised, sensitive data remains protected.
Managing API Access and Endpoints
Another best practice in securing API integrations is limiting the exposure of endpoints. An endpoint is a specific path through which an API can be accessed. The more endpoints that are publicly available, the greater the potential attack surface becomes. Organizations should carefully design their APIs so that only necessary endpoints are exposed. Internal functions that do not require external access should remain protected behind internal network controls.
Rate Limiting and Traffic Control
Rate limiting is also an important protective mechanism. Rate limiting controls how frequently a system can send requests to an API within a certain time period. This prevents excessive or malicious traffic from overwhelming the system. If a system suddenly sends thousands of requests in a short period of time, the API can temporarily block further requests. This helps protect against automated attacks and ensures that legitimate users continue to receive reliable service.
Monitoring and Logging Activity
Monitoring and logging play a vital role in maintaining API security over time. Every interaction with an API should be recorded in a secure log. These logs provide visibility into who accessed the system, when the request was made, and what data was requested. If unusual activity occurs, such as repeated failed authentication attempts or unexpected data requests, administrators can quickly investigate and respond. Continuous monitoring helps detect potential security threats before they cause damage.
Regular Security Reviews and Updates
Regular security reviews are another important aspect of protecting API integrations. As systems evolve and new integrations are added, security configurations must be reassessed. Credentials should be rotated periodically to reduce the risk of unauthorized access. Old integrations that are no longer used should be removed. By maintaining an active review process, organizations ensure that their security practices remain aligned with current operational needs.
Input Validation and Access Control
Secure API design also includes validating the data that enters the system. Input validation ensures that the information sent through the API follows expected formats and values. If a request contains unexpected or malicious input, the system can reject it before it affects internal processes. This practice protects systems from injection attacks and other forms of malicious manipulation.
Another important practice is the principle of least privilege. This principle means that systems and users should only receive the minimum level of access required to perform their tasks. When applied to API integrations, least privilege ensures that each integration can only access the specific data needed for its operation. Restricting access in this way reduces the potential impact of a security breach.
API Security in Field Service Operations
For organizations operating field service platforms, secure API integrations are especially important because service operations depend on accurate and reliable data exchange. A field service system may connect with customer management platforms to receive new service requests. It may integrate with accounting systems to generate invoices after job completion. Inventory systems may update spare part availability as technicians use parts in the field. If these integrations are not properly secured, sensitive operational data could be exposed or manipulated.
How Wello Supports Secure Integrations
Platforms such as Wello are designed with secure integration capabilities that allow service companies to connect their operational systems safely. Through structured APIs and controlled authentication mechanisms, the platform enables secure communication with external systems while maintaining strict control over data access. This ensures that service organizations can build connected digital workflows without compromising data protection.
Secure API integrations also support operational reliability. When systems communicate through well designed APIs, the information exchanged remains consistent and accurate. Work orders created in the service platform can automatically trigger updates in other systems. Customer records remain synchronized across platforms. Inventory updates reflect actual spare part usage in real time. These automated workflows reduce administrative effort and ensure that every department operates with accurate information.
Conclusion: Building Secure Connected Systems
As businesses continue to adopt cloud based platforms and digital infrastructure, the number of system integrations will continue to grow. Each new integration brings operational benefits but also introduces potential security risks. By following strong API security practices such as authentication, authorization, encryption, monitoring, and access control, organizations can maintain secure and reliable connections between their systems.
The goal of API security is not to restrict integration but to enable it safely. Secure integrations allow businesses to build connected digital environments where systems collaborate efficiently while protecting the data that drives daily operations. For service organizations managing complex workflows and distributed teams, this secure connectivity becomes a key component of operational success.
When implemented correctly, secure API integrations create a stable foundation for digital operations. They allow organizations to automate processes, synchronize information, and scale their infrastructure without exposing sensitive data. By investing in secure integration practices and platforms that support these capabilities, businesses ensure that their digital systems remain both powerful and protected.